CICD has become ubiquitous in almost every organization in one form or another to release code. This code could be application related or could be for provisioning the infrastructure.
Securing the CICD pipeline in cloud sprawl shouldn't be an afterthought. There are numerous threat vectors which could compromise a CICD pipeline. These threat vectors range from liberal IAM policies to overlooked auto-merge feature and from ignored build process to the ungoverned third party packages usage.
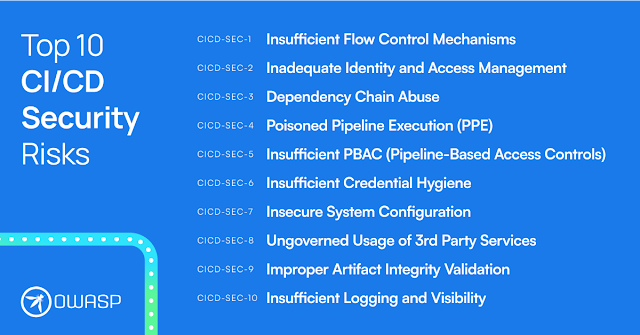
Here are Top 10 CI/CD Security Risks from Cider.
Cider says, that this document helps defenders identify focus areas for securing their CI/CD ecosystem. It is the result of extensive research into attack vectors associated with CI/CD, and the analysis of high profile breaches and security flaws. Numerous industry experts across multiple verticals and disciplines came together to collaborate on this document to ensure its relevance to today’s threat landscape, risk surface, and the challenges that defenders face in dealing with these risks.